Single Spülmaschinen repräsentieren eine maßgeschneiderte Lösung für kleinere Haushalte oder Singlepersonen, die allein leben. Diese kompakten Haushaltsgeräte sind das Ergebnis gezielter Forschung und Entwicklung, um den spezifischen Bedürfnissen von Nutzern mit begrenztem Platzangebot gerecht zu werden.

Sie zeichnen sich durch ihre hohe Effizienz bei der Reinigung von Geschirr und Besteck aus, ohne dabei wertvollen Küchenraum zu beanspruchen. Als Experten in der Entwicklung von Haushaltsgeräten bestätigen wir, dass Single Spülmaschinen eine optimale Balance zwischen Funktionalität und Platzersparnis bieten, was sie zu einer idealen Wahl für moderne, platzbewusste Küchen macht.
Menschen, die in kleinen Wohnungen, Studios oder WG-Zimmern wohnen, profitieren besonders von Single Spülmaschinen, da sie die Vorteile einer Spülmaschine nutzen können, ohne dabei Platzkompromisse eingehen zu müssen. Diese Geräte sind auch ideal für Berufstätige oder Studenten, die wenig Zeit haben, aber dennoch auf Sauberkeit und Komfort in ihrer Küche nicht verzichten möchten.
Welche sind die bestseller Single Spülmaschinen?
Bevor wir uns in die Details der verschiedenen Modelle vertiefen, werfen wir einen Blick auf die Bestseller Single Spülmaschinen, die auf dem Markt besonders gefragt sind.
Diese Modelle haben sich aufgrund ihrer herausragenden Eigenschaften und Leistung einen Namen gemacht und werden von vielen Menschen geschätzt, die nach einer effizienten und kompakten Lösung für ihre Spülbedürfnisse suchen.
- Bomann TSG 5701
- Midea ST 3.6F wi: Ein Tischgeschirrspüler mit 6 Waschprogrammen, Startzeitvorwahl, Extra Trocknungs-Funktion und IOT-Steuerung. Er ist ideal für kleine Räume
- Midea ST 5.31: Dieser Tischgeschirrspüler bietet extra viel Platz für große Teller und verfügt über eine Startzeitvorwahl von 1-24 Stunden
- COMFEE‘ Tischgeschirrspüler CTG 556N: Ein kompakter Tischgeschirrspüler mit Abmessungen von 438x550x500 mm, 6 Waschprogrammen und einem Schallleistungspegel von 49 dB(A). Er bietet Platz für 6 Maßgedecke.
- HAVA Tragbarer Mini Geschirrspüler: Ein leichter und tragbarer Mini-Geschirrspüler von HAVA, der sich durch seine einfache Bedienung auszeichnet und ideal für Campingurlaube oder kleine Küchen geeignet ist
Bomann® Mini Geschirrspüler TSG 5701

Der Bomann® TSG 5701 Mini Geschirrspüler ist ein kompakter und effizienter Geschirrspüler für kleinere Haushalte.
Mit Platz für bis zu 2 Maßgedecke ist er ideal für Singles oder Paare. Der Mini Geschirrspüler bietet verschiedene Programme, darunter Normal, ECO und Schnell.
Er verfügt auch über eine praktische Startzeitvorwahl und eine einfache Bedienung. Die Garantie und der Kundenservice für dieses Produkt können je nach Hersteller variieren.
Der Bomann® Mini Geschirrspüler ist die ideale Wahl für alle, die in ihrer kleinen Küche Platz sparen und dennoch nicht auf den Komfort einer Geschirrspülmaschine verzichten möchten. Mit seinen kompakten Abmessungen und seiner beeindruckenden Leistung bietet dieser Mini Geschirrspüler die perfekte Lösung für Singles, Paare oder kleine Haushalte.
Effiziente Reinigung für strahlend sauberes Geschirr
Trotz seiner kompakten Größe bietet der Bomann® Mini Geschirrspüler eine beeindruckende Reinigungsleistung. Mit seinem leistungsstarken Motor und den effektiven Sprüharmen werden selbst hartnäckige Verschmutzungen gründlich entfernt. Egal ob Teller, Gläser, Besteck oder Töpfe – dieser Mini Geschirrspüler liefert Ihnen stets strahlend sauberes Geschirr.
Platzsparendes Design für kleine Küchen
Der Bomann® Mini Geschirrspüler ist speziell für kleine Küchen konzipiert. Mit seinen kompakten Abmessungen passt er problemlos in jeden noch so begrenzten Raum. Dank seiner flexiblen Innenraumgestaltung finden Sie genügend Platz für Ihre Geschirrsammlung, ohne wertvollen Platz in Ihrer Küche zu beanspruchen.
Einfache Bedienung und vielseitige Programme
Die Bedienung des Bomann® Mini Geschirrspülers ist kinderleicht. Das übersichtliche Bedienfeld ermöglicht es Ihnen, die gewünschten Programme schnell und einfach auszuwählen. Sie können zwischen verschiedenen Spülmodi wie Normal, Intensiv, Schnell oder sogar einem Energiesparmodus wählen, um Ihre Bedürfnisse optimal anzupassen.
Leiser Betrieb für eine angenehme Küchenatmosphäre
Mit seinem leisen Betrieb sorgt der Bomann® Mini Geschirrspüler für eine angenehme Küchenatmosphäre. Sie können Ihre Geschirrreinigung genießen, ohne von lästigen Geräuschen gestört zu werden. Damit ist dieser Mini Geschirrspüler auch ideal für offene Wohnküchen oder kleine Apartments geeignet.
Sparen Sie Zeit und Mühe mit dem Bomann® Mini Geschirrspüler und genießen Sie den Komfort einer Geschirrspülmaschine auch in Ihrer kleinen Küche! Bestellen Sie noch heute und erleichtern Sie sich Ihren Küchenalltag.
Pro
- Kompakte Größe für kleinere Haushalte
- Verschiedene Programme
- Einfache Bedienung
Contra
- Begrenztes Fassungsvermögen von 2 Maßgedecken
Midea ST 3.6F wi

Effiziente Reinigung für strahlend sauberes Geschirr Die Midea ST 3.6F wi Spülmaschine bietet eine effiziente Reinigungstechnologie, die Ihr Geschirr mühelos sauber und glänzend macht. Dank ihres leistungsstarken Motors und der innovativen Sprüharme werden selbst hartnäckige Verschmutzungen spielend entfernt. Egal, ob es sich um fettige Pfannen, eingetrocknete Speisereste oder empfindliches Glas handelt, diese Spülmaschine liefert immer beste Ergebnisse.
Intuitive Bedienung für maximalen Komfort
Mit der Midea ST 3.6F wi Spülmaschine wird das Spülen zum Kinderspiel. Das übersichtliche Bedienfeld ermöglicht Ihnen eine einfache Navigation und Auswahl der gewünschten Programme. Sie können zwischen verschiedenen Spülmodi wie Schnellspülen, Intensivspülen oder Eco-Modus wählen, um Ihre Bedürfnisse optimal anzupassen. Darüber hinaus verfügt die Spülmaschine über eine praktische Startzeitvorwahl, sodass Sie den Spülvorgang ganz nach Ihrem Zeitplan planen können.

Platz für Ihre gesamte Geschirrsammlung
Mit einem großzügigen Innenraum bietet die Midea ST 3.6F wi Spülmaschine ausreichend Platz für Ihre gesamte Geschirrsammlung. Das flexible und verstellbare Innenraumdesign ermöglicht es Ihnen, Teller, Tassen, Besteck und Töpfe problemlos zu arrangieren. So können Sie immer das Maximum aus jeder Spülung herausholen.
Energieeffizient und leise im Betrieb
Die Midea ST 3.6F wi Spülmaschine ist nicht nur leistungsstark, sondern auch energieeffizient. Mit ihrer ausgeklügelten Technologie sorgt sie für einen geringen Wasserverbrauch und niedrige Energiekosten. Darüber hinaus arbeitet sie äußerst leise, sodass Sie sich während des Spülens nicht gestört fühlen.
Der Midea ST 3.6F wi ist ein leistungsstarker Mini-Geschirrspüler mit modernen Funktionen. Er bietet Platz für bis zu 6 Maßgedecke und verfügt über verschiedene Programme zur Auswahl, darunter Normal, Intensiv, ECO und Schnell.
Der ST 3.6F wi zeichnet sich durch eine hohe Energieeffizienz aus und verfügt über eine praktische Startzeitvorwahl. Midea bietet eine Garantie von 2 Jahren auf den Geschirrspüler und ihr Kundenservice ist bekannt für seine Zuverlässigkeit und Hilfsbereitschaft.
Pro
- Großes Fassungsvermögen für bis zu 6 Maßgedecke
- Verschiedene Programme zur Auswahl
- Hohe Energieeffizienz
- Praktische Startzeitvorwahl
- Zuverlässige Garantie von 2 Jahren
Contra
- Höherer Preis im Vergleich zu kleineren Modellen
Midea ST 5.31 Mini Geschirrspüler

Der Midea ST 5.31 Mini Geschirrspüler bietet Platz für bis zu 6 Maßgedecke und ist mit verschiedenen Programmen ausgestattet, darunter Normal, ECO, Schnell und Vorspülen.
Der Geschirrspüler zeichnet sich durch eine hohe Energieeffizienz aus und verfügt über eine praktische Startzeitvorwahl und eine Restzeitanzeige.

Der Midea ST 5.31 Mini Geschirrspüler ist die perfekte Lösung für alle, die in ihrer kleinen Küche Platz sparen möchten, aber dennoch nicht auf die Vorteile einer Geschirrspülmaschine verzichten wollen. Mit seiner kompakten Größe und beeindruckenden Leistung bietet dieser Mini Geschirrspüler eine effiziente und zeitsparende Lösung für den Abwasch.

Effiziente Reinigung für glänzend sauberes Geschirr
Trotz seiner kompakten Größe überzeugt der Midea ST 5.31 Mini Geschirrspüler mit einer beeindruckenden Reinigungsleistung. Mit seinem leistungsstarken Motor und den effektiven Sprüharmen werden selbst hartnäckige Verschmutzungen gründlich entfernt. Ganz gleich, ob es sich um Teller, Gläser, Besteck oder Töpfe handelt, dieser Mini Geschirrspüler sorgt für glänzend sauberes Geschirr.
Platzsparendes Design für kleine Küchen
Der Midea ST 5.31 Mini Geschirrspüler ist speziell für kleine Küchen konzipiert. Mit seinen kompakten Abmessungen passt er problemlos in jede Ecke Ihrer Küche. Trotz der geringen Größe bietet er ausreichend Platz für Ihr Geschirr, sodass Sie effizient spülen können, ohne wertvollen Platz zu verschwenden.
Benutzerfreundliche Bedienung und vielseitige Programme
Die Bedienung des Midea ST 5.31 Mini Geschirrspülers ist denkbar einfach. Mit dem übersichtlichen Bedienfeld können Sie problemlos zwischen verschiedenen Spülprogrammen wählen, um Ihre Bedürfnisse anzupassen. Ob Normal, Intensiv oder Schnell – dieser Mini Geschirrspüler bietet für jede Art von Geschirr die passende Reinigungsoption.
Leiser Betrieb für eine angenehme Küchenatmosphäre
Mit seinem leisen Betrieb sorgt der Midea ST 5.31 Mini Geschirrspüler für eine angenehme Küchenatmosphäre. Sie können Ihre Geschirrreinigung genießen, ohne von störenden Geräuschen gestört zu werden. Dies macht ihn besonders geeignet für offene Wohnküchen oder kleine Apartments.
Pro
- Großes Fassungsvermögen für bis zu 6 Maßgedecke
- Verschiedene Programme zur Auswahl
- Hohe Energieeffizienz
- Praktische Startzeitvorwahl
Contra
- k.A.
COMFEE‘ Tischgeschirrspüler CTG 556N

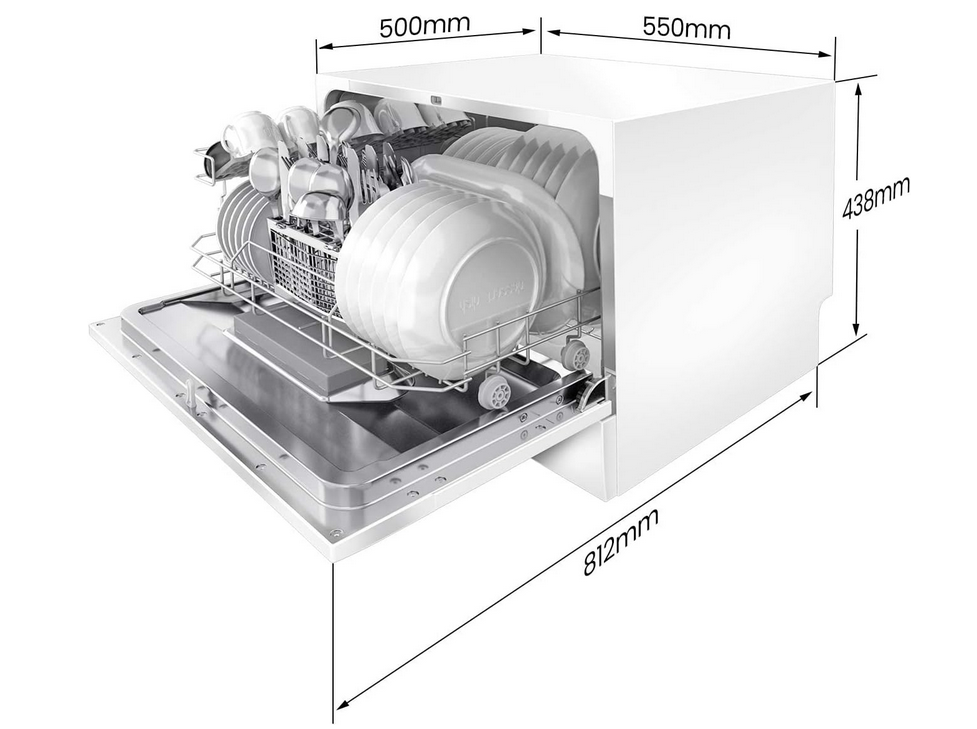
Der COMFEE‘ Tischgeschirrspüler CTG 556N bietet Platz für bis zu 6 Maßgedecke und verfügt über verschiedene Programme, darunter Normal, ECO und Schnell. Der Geschirrspüler ist einfach zu bedienen und zeichnet sich durch seine Energieeffizienz aus. Er bietet auch eine praktische Startzeitvorwahl und eine Restzeitanzeige.
Der COMFEE‘ Tischgeschirrspüler CTG 556N ist die ideale Wahl für alle, die in ihrer Küche Platz sparen möchten und dennoch nicht auf die Vorteile einer Geschirrspülmaschine verzichten wollen. Mit seinem kompakten Design und seiner beeindruckenden Leistung bietet dieser Tischgeschirrspüler eine effiziente und praktische Lösung für die Reinigung Ihres Geschirrs.

Effiziente Reinigung für glänzend sauberes Geschirr
Trotz seiner kompakten Größe überzeugt der COMFEE‘ Tischgeschirrspüler CTG 556N mit einer beeindruckenden Reinigungsleistung. Mit seinem leistungsstarken Motor und den effektiven Sprüharmen werden selbst hartnäckige Verschmutzungen gründlich entfernt. Egal ob Teller, Gläser, Besteck oder Töpfe – dieser Tischgeschirrspüler sorgt für glänzend sauberes Geschirr.
Platzsparendes Design für jede Küche
Der COMFEE‘ Tischgeschirrspüler CTG 556N ist speziell für kleine Küchen, Büros oder Wohnungen mit begrenztem Platz konzipiert. Dank seines kompakten Designs passt er problemlos auf jeden Tisch oder in jede Ecke Ihrer Küche. Damit sparen Sie wertvollen Raum, während Sie den Komfort einer Geschirrspülmaschine genießen können.
Benutzerfreundliche Bedienung und vielseitige Programme
Die Bedienung des COMFEE‘ Tischgeschirrspülers CTG 556N ist denkbar einfach. Mit dem übersichtlichen Bedienfeld können Sie die gewünschten Programme schnell und unkompliziert auswählen. Sie haben die Wahl zwischen verschiedenen Spülmodi wie Normal, Intensiv, Schnell oder sogar einem Energiesparmodus, um Ihre Bedürfnisse optimal anzupassen.
Leiser Betrieb für eine angenehme Umgebung
Der COMFEE‘ Tischgeschirrspüler CTG 556N arbeitet besonders leise, sodass Sie Ihre Küchenatmosphäre in vollen Zügen genießen können. Sie können den Geschirrspüler laufen lassen, ohne von störenden Geräuschen gestört zu werden. Dies ist besonders praktisch für Büros oder offene Wohnküchen, in denen Ruhe und Komfort wichtig sind.
Sparen Sie Zeit und Aufwand mit dem COMFEE‘ Tischgeschirrspüler CTG 556N und erleben Sie die Freude an sauberem Geschirr in Ihrer Küche. Bestellen Sie noch heute und genießen Sie den Komfort und die Effizienz dieses platzsparenden Tischgeschirrspülers!
Pro
- Großes Fassungsvermögen für bis zu 6 Maßgedecke
- Verschiedene Programme zur Auswahl
- Energieeffizient
- Praktische Startzeitvorwahl
Contra
- Garantie und Kundenservice können je nach Hersteller variieren
HAVA Tragbarer Mini Geschirrspüler – Die praktische Lösung für unterwegs!


Der HAVA Tragbare Mini Geschirrspüler ist eine praktische Option für den Einsatz in kleinen Küchen oder bei begrenztem Platz. Er bietet Platz für bis zu 4 Maßgedecke und verfügt über verschiedene Programme, darunter Normal, ECO und Schnell. Der tragbare Geschirrspüler ist einfach zu bedienen und verfügt über eine praktische Startzeitvorwahl
Der HAVA Tragbarer Mini Geschirrspüler ist die ideale Wahl für alle, die auch unterwegs nicht auf die Vorteile einer Geschirrspülmaschine verzichten möchten. Mit seiner kompakten Größe und seinem portablen Design bietet dieser Mini Geschirrspüler eine effiziente und bequeme Lösung für die Reinigung Ihres Geschirrs, egal wo Sie sich befinden.
Effiziente Reinigung für strahlend sauberes Geschirr
Trotz seiner kompakten Größe überzeugt der HAVA Tragbarer Mini Geschirrspüler mit einer beeindruckenden Reinigungsleistung. Mit seinem leistungsstarken Motor und den effektiven Sprüharmen werden selbst hartnäckige Verschmutzungen gründlich entfernt. Ob Teller, Gläser, Besteck oder Töpfe – dieser Mini Geschirrspüler sorgt immer für strahlend sauberes Geschirr, egal wo Sie gerade sind.
Tragbares Design für maximale Flexibilität
Der HAVA Tragbarer Mini Geschirrspüler wurde speziell für den mobilen Einsatz entwickelt. Mit seinem kompakten und leichten Design können Sie ihn problemlos überallhin mitnehmen. Egal, ob Sie ihn im Wohnmobil, auf einem Boot, im Büro oder beim Camping verwenden möchten – dieser Mini Geschirrspüler ist immer einsatzbereit und erleichtert Ihnen die Geschirrreinigung unterwegs.
Einfache Bedienung und vielseitige Programme
Die Bedienung des HAVA Tragbaren Mini Geschirrspülers ist denkbar einfach. Mit dem übersichtlichen Bedienfeld können Sie problemlos zwischen verschiedenen Spülprogrammen wählen, um Ihre Bedürfnisse anzupassen. Sie können zwischen verschiedenen Modi wie Normal, Schnell oder sogar einem energiesparenden Modus wählen, um Ihren Anforderungen gerecht zu werden.
USB-Aufladung für flexible Nutzung
Der HAVA Tragbare Mini Geschirrspüler wird über USB aufgeladen, was ihm maximale Flexibilität verleiht. Sie können ihn ganz einfach an eine Powerbank, einen Laptop oder andere USB-Stromquellen anschließen. Dadurch können Sie den Geschirrspüler auch in Umgebungen ohne direkten Stromanschluss verwenden.
Erleben Sie die Bequemlichkeit und Effizienz des HAVA Tragbaren Mini Geschirrspülers und genießen Sie sauberes Geschirr, egal wo Sie sich gerade befinden. Bestellen Sie noch heute und machen Sie die Geschirrreinigung unterwegs zum Kinderspiel!
Pro
- Tragbare Option für begrenzten Platz
- Verschiedene Programme
- Einfache Bedienung
Contra
- Garantie und Kundenservice können je nach Hersteller variieren
Beim Thema platzsparende Küchengeräte darf der Minibackofen und Mini Mikrowellen nicht fehlen.
Vorteile von Single Spülmaschinen
Single Spülmaschinen bieten eine Reihe von Vorteilen, die sie zu einer attraktiven Option für kleine Haushalte machen:
- Platzsparendes Design: Dank ihrer kompakten Größe passen Single Spülmaschinen problemlos in kleine Küchen oder sogar in Wohnungen mit begrenztem Platzangebot.
- Zeiteinsparung: Die Automatisierung des Spülprozesses ermöglicht es Ihnen, Zeit für andere Aktivitäten zu nutzen, anstatt das Geschirr von Hand zu spülen.
- Energie- und Wassereffizienz: Single Spülmaschinen sind darauf ausgelegt, Energie und Wasser zu sparen, was sowohl die Umwelt als auch Ihre Energiekosten schont.
- Sauberes Geschirr: Dank der fortschrittlichen Spültechnologie und der verschiedenen Reinigungsprogramme können Single Spülmaschinen Ihr Geschirr gründlich und hygienisch reinigen.
- Komfort und Bequemlichkeit: Sie müssen nicht mehr mühsam das Geschirr abwaschen. Stattdessen können Sie es einfach in die Single Spülmaschine stellen und den Rest erledigen lassen.
Platzsparend
Eine der Hauptvorteile einer Single Spülmaschine ist ihr platzsparendes Design. Durch ihre kompakte Größe nimmt sie deutlich weniger Platz ein als herkömmliche Geschirrspüler. Damit ist sie ideal für kleine Küchen oder Wohnräume, in denen jeder Quadratzentimeter zählt.
Single Spülmaschinen können problemlos in Küchenzeilen integriert oder als freistehende Geräte aufgestellt werden. Selbst in kleinsten Küchen findet sich oft ein Platz für diese praktischen Helfer. Sie bieten die perfekte Lösung, wenn Sie den Komfort eines Geschirrspülers genießen möchten, ohne viel Platz zu opfern.
Zudem sind viele Modelle so konzipiert, dass sie nicht nur unter der Arbeitsplatte, sondern auch in einem Hochschrank eingebaut werden können. Damit bieten sie zusätzliche Flexibilität bei der Küchengestaltung und ermöglichen es, den verfügbaren Platz optimal zu nutzen.
Durch den Kauf einer Single Spülmaschine können Sie also eine voll funktionsfähige Geschirrspülmaschine in Ihrer Küche unterbringen, ohne Abstriche bei Raum oder Design machen zu müssen.
Energie- und Wassereffizienz
Energie- und Wassereffizienz sind weitere entscheidende Vorteile von Single Spülmaschinen. Diese Geräte sind darauf ausgelegt, mit geringerem Wasserverbrauch und weniger Energie auszukommen als herkömmliche Geschirrspülmaschinen.
- Wassereffizienz: Im Vergleich zum manuellen Abwaschen sparen Single Spülmaschinen eine erhebliche Menge an Wasser. Während man für das Spülen per Hand oft mehrere Liter Wasser benötigt, verbrauchen moderne Single Spülmaschinen nur wenige Liter pro Spülgang. Dies ist nicht nur gut für die Umwelt, sondern hilft auch, Ihre Wasserrechnung niedrig zu halten.
- Energieeffizienz: Auch in puncto Energieverbrauch punkten Single Spülmaschinen. Durch ihre kleinere Größe und effiziente Technologie verbrauchen sie weniger Energie als größere Geschirrspülmaschinen. Viele Modelle verfügen zudem über eine hohe Energieeffizienzklasse (A++ oder sogar A+++), die einen besonders sparsamen Betrieb garantiert.
- Öko-Programme: Viele Single Spülmaschinen bieten zusätzlich spezielle Öko- oder Sparprogramme. Diese Programme sind auf einen möglichst geringen Wasser- und Energieverbrauch ausgelegt, ohne dass Sie Abstriche bei der Reinigungsleistung machen müssen.
Durch den Kauf einer energie- und wassereffizienten Single Spülmaschine können Sie also nicht nur Ihren ökologischen Fußabdruck reduzieren, sondern auch langfristig Geld sparen. Ein echter Gewinn für Sie und die Umwelt!
Ideal für Ein-Personen-Haushalte
Wenn Sie alleine leben oder generell nicht viel Geschirr ansammeln, ist eine Single Spülmaschine die perfekte Wahl. Sie ist effizient, handlich und kann Ihren Alltag erheblich erleichtern.
Bequemlichkeit
Wenn es um Bequemlichkeit geht, haben Single Spülmaschinen eindeutig die Nase vorn. Wer kennt es nicht – nach einem langen Arbeitstag oder einem gemütlichen Abendessen mit Freunden wartet der ungeliebte Abwasch. Mit einer Single Spülmaschine gehört dieses Problem der Vergangenheit an.
- Zeitersparnis: Eine der größten Bequemlichkeiten einer Single Spülmaschine ist die Zeitersparnis. Statt mühsam per Hand zu spülen, können Sie das schmutzige Geschirr einfach in die Maschine einräumen, das gewünschte Programm wählen und den Rest der Arbeit dem Gerät überlassen. Während die Maschine läuft, haben Sie Zeit für die Dinge, die Ihnen wirklich wichtig sind.
- Einfache Bedienung: Moderne Single Spülmaschinen zeichnen sich durch eine besonders benutzerfreundliche Bedienung aus. Übersichtliche Bedienfelder und eine Vielzahl von Spülprogrammen ermöglichen eine einfache und individuelle Anpassung an Ihren Geschirrspülbedarf.
- Kein Abtrocknen: Ein weiterer Vorteil ist, dass das Geschirr nach dem Spülgang bereits trocken ist. Das lästige Abtrocknen per Hand entfällt also.
- Sauberkeit und Hygiene: Single Spülmaschinen reinigen nicht nur effektiv, sondern auch hygienisch. Mit hohen Temperaturen und speziellen Spülprogrammen entfernen sie auch hartnäckige Speisereste und Bakterien zuverlässig.
Eine Single Spülmaschine vereinfacht also den Alltag erheblich und ermöglicht es Ihnen, mehr Zeit mit angenehmeren Dingen zu verbringen. Und seien wir ehrlich – wer wünscht sich das nicht?
Hygiene
Ein weiterer wichtiger Aspekt, der für den Kauf einer Single Spülmaschine spricht, ist die Hygiene. Geschirrspülmaschinen reinigen das Geschirr gründlicher und hygienischer als der manuelle Abwasch. Dies liegt an den hohen Temperaturen, die während des Spülvorgangs erreicht werden, und der Verwendung von speziellen Reinigungs- und Klarspülmitteln.
- Hohe Temperaturen: Geschirrspülmaschinen können Temperaturen von bis zu 70 Grad Celsius erreichen. Diese hohen Temperaturen sind in der Lage, fast alle Bakterien und Viren zu töten, die auf dem Geschirr vorhanden sein könnten. Beim manuellen Abwasch hingegen werden in der Regel niedrigere Temperaturen verwendet, was die Effektivität der Bakterienvernichtung verringert.
- Keine Kreuzkontamination: Bei der Handwäsche kann es leicht zu einer Kreuzkontamination kommen, wenn dasselbe Spültuch oder derselbe Schwamm für verschiedene Teile des Geschirrs verwendet wird. Geschirrspülmaschinen hingegen reinigen jedes Stück Geschirr einzeln und verhindern so eine Kreuzkontamination.
- Trockenfunktion: Viele Single Spülmaschinen bieten zudem eine Trockenfunktion. Dies ist ein weiterer wichtiger Aspekt, wenn es um Hygiene geht, da Bakterien in feuchten Umgebungen gedeihen. Durch das Trocknen des Geschirrs in der Spülmaschine wird das Wachstum von Bakterien verhindert.
- Effektive Reinigungsmittel: Single Spülmaschinen nutzen spezielle Reinigungs- und Klarspülmittel, die dazu beitragen, Geschirr und Besteck effektiv von Essensresten zu befreien und sie strahlend sauber und hygienisch rein zu hinterlassen.
Wenn Sie also Wert auf Sauberkeit und Hygiene legen, ist eine Single Spülmaschine eine hervorragende Wahl. Sie stellt sicher, dass Ihr Geschirr nicht nur optisch sauber, sondern auch hygienisch rein ist.
Zeiteinsparung
Eine der größten Bequemlichkeiten, die eine Single Spülmaschine bietet, ist ohne Zweifel die Zeiteinsparung. Im stressigen Alltag bleibt oft wenig Zeit für Hausarbeiten wie das Spülen von Geschirr. Mit einer Single Spülmaschine können Sie jedoch wertvolle Minuten, wenn nicht sogar Stunden, sparen.
- Automatischer Abwasch: Statt Geschirr und Besteck per Hand zu spülen, laden Sie einfach alles in die Spülmaschine, wählen das passende Programm und lassen die Maschine die Arbeit erledigen. Während die Spülmaschine läuft, können Sie sich anderen Aufgaben widmen oder einfach entspannen.
- Kein Vorwaschen erforderlich: Moderne Spülmaschinen sind so effizient, dass in der Regel kein Vorwaschen erforderlich ist. Sie können also direkt das benutzte Geschirr einräumen, ohne es vorher abspülen zu müssen. Dies spart zusätzlich Zeit und Wasser.
- Zeitplanung: Die meisten Single Spülmaschinen verfügen über eine Startzeitvorwahl. So können Sie das Spülprogramm zu einem Zeitpunkt starten lassen, der Ihnen am besten passt – beispielsweise nachts, wenn der Strompreis niedriger ist, oder während Sie bei der Arbeit sind.
Durch die Verwendung einer Single Spülmaschine haben Sie also mehr Zeit für die Dinge, die Sie wirklich genießen. Ob es das Lesen eines guten Buches, das Schauen Ihrer Lieblingsserie oder das Verbringen von Zeit mit Freunden und Familie ist – mit einer Single Spülmaschine haben Sie mehr Freizeit in Ihrem Alltag.
Wichtige Funktionen und Eigenschaften
Neben den bereits erwähnten Vorteilen bieten Single Spülmaschinen auch eine Vielzahl von Funktionen, die den Gebrauch noch komfortabler und effizienter machen.
- Verschiedene Spülprogramme: Die meisten Single Spülmaschinen verfügen über mehrere Spülprogramme. Diese reichen von intensiven Programmen für stark verschmutztes Geschirr bis hin zu sanften Programmen für empfindliches Geschirr. Einige Modelle bieten sogar spezielle Programme für Gläser oder einen Schnellspülgang.
- Automatische Programme: Einige Single Spülmaschinen verfügen über automatische Programme. Diese passen die Wasserhärte, die Temperatur und die Spüldauer automatisch an den Verschmutzungsgrad des Geschirrs an. Dadurch wird das Geschirr optimal gereinigt und gleichzeitig Wasser und Energie gespart.
- Beladungserkennung: Eine Funktion, die bei vielen Modellen Standard ist, ist die Beladungserkennung. Die Maschine erkennt, wie stark sie beladen ist, und passt den Wasser- und Energieverbrauch entsprechend an.
- Startzeitvorwahl: Mit der Startzeitvorwahl können Sie den Start des Spülprogramms nach Ihren Wünschen planen. Dies kann besonders praktisch sein, wenn Sie die Maschine laufen lassen möchten, während Sie nicht zu Hause sind oder nachts, um von niedrigeren Strompreisen zu profitieren.
- Trocknungsfunktionen: Viele Single Spülmaschinen verfügen über Trocknungsfunktionen, die dafür sorgen, dass Ihr Geschirr am Ende des Spülgangs trocken ist. Einige Modelle bieten sogar eine automatische Türöffnung am Ende des Spül- und Trocknungszyklus, um das Trocknungsergebnis zu verbessern.
Mit diesen vielfältigen Funktionen wird die Benutzung einer Single Spülmaschine zum Kinderspiel und trägt dazu bei, Ihren Alltag erheblich zu erleichtern.
Verschiedene Spülprogramme
Einer der großen Vorteile von Single Spülmaschinen sind die zahlreichen Spülprogramme, die sie bieten. Diese Programme sind speziell darauf ausgelegt, unterschiedliche Arten von Geschirr und Verschmutzungen effektiv zu behandeln, und bieten daher für jede Situation die richtige Lösung.
- Intensivprogramm: Dieses Programm ist ideal für stark verschmutztes Geschirr und Töpfe. Es reinigt mit hohen Temperaturen und einem starken Wasserdruck, um auch hartnäckige Speisereste zu entfernen.
- Eco- oder Sparprogramm: Diese Programme sind auf Energie- und Wassersparsamkeit ausgelegt. Sie reinigen mit niedrigeren Temperaturen und verlängerten Spülzeiten, was den Energie- und Wasserverbrauch reduziert.
- Automatik- oder Sensorprogramm: Diese Programme passen den Spülzyklus automatisch an die Menge und den Verschmutzungsgrad des Geschirrs an. Sensoren messen die Trübung des Wassers und stellen die Spülparameter entsprechend ein.
- Schnell- oder Kurzprogramm: Diese Programme sind ideal, wenn Sie schnell sauberes Geschirr benötigen. Sie reinigen in kürzerer Zeit, sind jedoch in der Regel nicht für stark verschmutztes Geschirr geeignet.
- Gläser- oder Feinprogramm: Diese Programme reinigen bei niedrigen Temperaturen und mit einem sanften Wasserdruck. Sie sind ideal für empfindliches Geschirr wie Gläser oder Porzellan.
- Vorspül- oder Einweichprogramm: Dieses Programm eignet sich zum Einweichen von stark verschmutztem Geschirr, bevor ein Hauptspülprogramm durchgeführt wird.
Kaufkriterien Single Spülmaschinen
Bevor Sie eine Single Spülmaschine kaufen, sollten Sie folgende Überlegungen anstellen:
Raum und Platzbedarf
Bevor Sie eine Single Spülmaschine kaufen, ist es wichtig, sorgfältig über den verfügbaren Raum und den Platzbedarf in Ihrer Küche nachzudenken. Hier sind einige Überlegungen, die Sie bei der Anschaffung einer Single Spülmaschine berücksichtigen sollten:
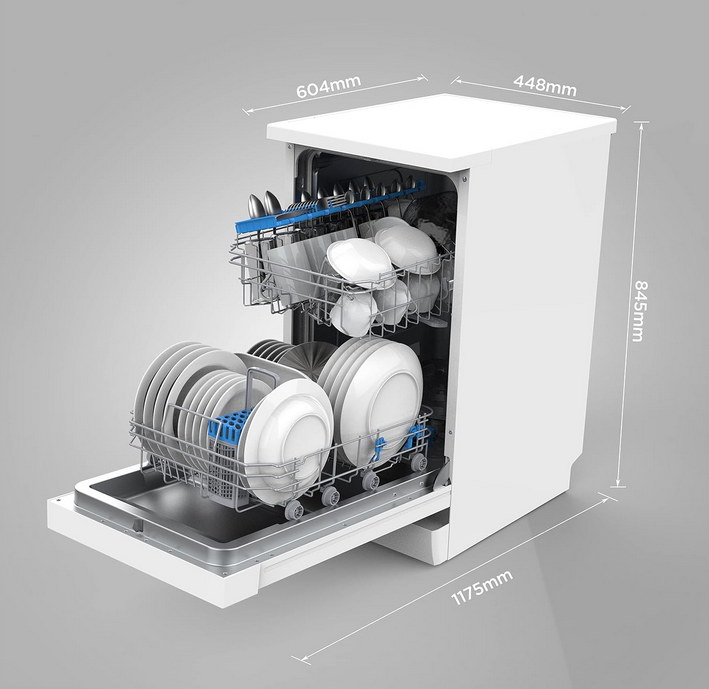
- Messungen des verfügbaren Raums: Messen Sie den Bereich in Ihrer Küche, in dem Sie die Single Spülmaschine platzieren möchten. Berücksichtigen Sie die Breite, Höhe und Tiefe des Raums, um sicherzustellen, dass die Spülmaschine gut passt und ausreichend Platz für die Beladung und Entladung des Geschirrs vorhanden ist.
- Freiraum für die Luftzirkulation: Single Spülmaschinen benötigen ausreichend Platz für die Luftzirkulation, insbesondere an den Seiten und an der Rückseite des Geräts. Stellen Sie sicher, dass Sie genügend Freiraum um die Spülmaschine herum lassen, um eine ordnungsgemäße Belüftung zu ermöglichen und eine Überhitzung zu vermeiden.
- Platz für den Wasseranschluss und den Abfluss: Überprüfen Sie die Position des Wasseranschlusses und des Abflusses in Ihrer Küche. Stellen Sie sicher, dass Sie einen geeigneten Wasseranschluss in der Nähe des Installationsortes haben und dass ein Abfluss vorhanden ist, um den Abwasserschlauch der Spülmaschine anzuschließen.
- Arbeitsfläche für die Beladung und Entladung: Stellen Sie sicher, dass Sie ausreichend Arbeitsfläche in der Nähe der Single Spülmaschine haben, um das Geschirr vorzubereiten, zu beladen und zu entladen. Eine ausreichend große Arbeitsfläche erleichtert die Handhabung des Geschirrs und ermöglicht eine bequeme Nutzung der Spülmaschine.
- Erforderliche Höhe der Arbeitsplatte: Überprüfen Sie, ob die Höhe der Arbeitsplatte in Ihrer Küche mit der Höhe der Single Spülmaschine kompatibel ist. Einige Single Spülmaschinen können unter einer Standard-Arbeitsplatte installiert werden, während andere möglicherweise eine spezielle Anpassung oder eine erhöhte Arbeitsfläche erfordern.
- Einbaufähigkeit oder freistehendes Modell: Entscheiden Sie, ob Sie eine freistehende Single Spülmaschine oder ein einbaufähiges Modell bevorzugen. Einbaufähige Modelle können nahtlos in Ihre Küchenzeile integriert werden, während freistehende Modelle flexibler in der Platzierung sind.
Durch die sorgfältige Planung des Raum- und Platzbedarfs können Sie sicherstellen, dass die Single Spülmaschine gut in Ihre Küche passt und effizient genutzt werden kann. Beachten Sie, dass die genauen Maße und Spezifikationen je nach Modell variieren können. Lesen Sie daher die Produktbeschreibungen und technischen Daten sorgfältig durch, um sicherzustellen, dass die ausgewählte Single Spülmaschine zu Ihrem verfügbaren Raum passt.
Tipps zur Pflege und Wartung
Die regelmäßige Pflege und Wartung Ihrer Single Spülmaschine trägt dazu bei, ihre Leistung und Lebensdauer zu erhalten. Hier sind einige wichtige Tipps, um Ihre Spülmaschine in einem optimalen Zustand zu halten:
- Reinigung des Innenraums: Entfernen Sie regelmäßig Speisereste und Verunreinigungen aus dem Innenraum Ihrer Spülmaschine. Achten Sie dabei besonders auf die Filter, den Sprüharm und die Türdichtung. Verwenden Sie dafür einen weichen Lappen oder eine Bürste und warmes Seifenwasser. Vermeiden Sie scharfe Reinigungsmittel oder Scheuerschwämme, da sie das Material beschädigen können.
- Entkalkung: Kalkablagerungen können die Leistung Ihrer Spülmaschine beeinträchtigen. Verwenden Sie regelmäßig einen speziellen Entkalker, der für Spülmaschinen geeignet ist, um Kalkablagerungen zu entfernen. Befolgen Sie dabei die Anweisungen des Herstellers.
- Beladung: Achten Sie darauf, dass Sie die Spülmaschine nicht überladen. Überfüllte Körbe können zu unzureichender Reinigung führen und die Sprüharme blockieren. Stellen Sie sicher, dass die Geschirrteile genügend Platz haben, um das Wasser frei zu erreichen.
- Richtiges Einräumen: Platzieren Sie das Geschirr und das Besteck so, dass es nicht miteinander verhakt oder sich gegenseitig blockiert. Richten Sie Teller und Tassen schräg, damit das Wasser besser abfließen kann und eine gleichmäßige Reinigung gewährleistet ist.
- Verwendung von Spülmittel: Verwenden Sie nur spezielles Spülmittel für Geschirrspülmaschinen und dosieren Sie es entsprechend den Angaben des Herstellers. Übermäßige Menge an Spülmittel kann zu übermäßiger Schaumbildung führen und die Leistung der Spülmaschine beeinträchtigen.
- Regelmäßige Inspektion: Überprüfen Sie regelmäßig die Sprüharme, die Dichtungen und die Wasserzufuhrschläuche auf Verschleiß oder Verstopfung. Reinigen oder ersetzen Sie diese Teile bei Bedarf, um eine optimale Leistung zu gewährleisten.
- Achten Sie auf Undichtigkeiten: Kontrollieren Sie regelmäßig, ob es Undichtigkeiten oder Wasseransammlungen um die Spülmaschine herum gibt. Dies kann auf defekte Dichtungen oder Leitungen hinweisen, die repariert werden müssen.
Durch regelmäßige Pflege und Wartung können Sie die Leistung und Langlebigkeit Ihrer Single Spülmaschine gewährleisten. Befolgen Sie diese Tipps und lesen Sie auch die Anweisungen des Herstellers, um Ihre Spülmaschine optimal zu pflegen.
Häufig gestellte Fragen (FAQs)
Gibt es Single Spülmaschinen mit integrierter Trocknungsfunktion?
Ja, es gibt Single Spülmaschinen, die über eine integrierte Trocknungsfunktion verfügen. Die Trocknungsfunktion ist ein wichtiger Aspekt bei der Auswahl einer Spülmaschine, da sie dafür sorgt, dass das Geschirr nach dem Spülvorgang trocken und einsatzbereit ist.
Kann ich empfindliches Geschirr wie Porzellan in einer Single Spülmaschine reinigen?
Ja, es ist in der Regel möglich, empfindliches Geschirr wie Porzellan in einer Single Spülmaschine zu reinigen, vorausgesetzt, Sie beachten bestimmte Vorsichtsmaßnahmen. Hier sind einige Tipps, wie Sie empfindliches Geschirr schonend in Ihrer Spülmaschine reinigen können:
Wie viel Wasser verbraucht eine Single Spülmaschine pro Spülgang?
Der genaue Wasserverbrauch einer Single Spülmaschine kann je nach Modell und Hersteller variieren. In der Regel liegt der durchschnittliche Wasserverbrauch einer Single Spülmaschine pro Spülgang jedoch zwischen 8 und 15 Litern. Es ist wichtig zu beachten, dass moderne Spülmaschinen zunehmend energie- und wassersparende Funktionen integrieren, um den Verbrauch zu minimieren.
Wie lange dauert ein Spülgang bei einer Single Spülmaschine?
Die Dauer eines Spülgangs bei einer Single Spülmaschine kann je nach Modell, gewähltem Programm und Beladung variieren. Im Allgemeinen dauert ein typischer Spülgang bei einer Single Spülmaschine zwischen 60 und 120 Minuten. Moderne Spülmaschinen sind mit verschiedenen Programmen ausgestattet, die unterschiedliche Spüldauer und Reinigungseffizienz bieten.
Können Single Spülmaschinen auch Besteck reinigen?
Ja, Single Spülmaschinen können auch Besteck effektiv reinigen. Besteck, wie Messer, Gabeln und Löffel, kann sicher in einer Single Spülmaschine gereinigt werden.
Was ist der Unterschied zwischen Single Spülmaschinen und Standard-Spülmaschinen?
Single Spülmaschinen, auch bekannt als Mini-Spülmaschinen oder Tischgeschirrspüler, unterscheiden sich in einigen wichtigen Aspekten von Standard-Spülmaschinen.
Wie viel Geschirr passt in eine Single Spülmaschine?
Die Kapazität einer Single Spülmaschine variiert je nach Modell, kann aber in der Regel etwa 6 bis 8 Maßgedecke aufnehmen. Ein Maßgedeck besteht typischerweise aus einem flachen Teller, einem Suppenteller, einem Dessertteller, einem Glas, einer Tasse, einem Unterteller, einem Messer, einer Gabel, einem Löffel und einem Teelöffel.
Sind Single Spülmaschinen energieeffizient?
Ja, Single Spülmaschinen können energieeffizient sein. Moderne Single Spülmaschinen sind darauf ausgelegt, den Energieverbrauch zu minimieren und umweltfreundlicher zu sein.
Die Wahl einer energieeffizienten Single Spülmaschine kann nicht nur dazu beitragen, Energie zu sparen, sondern auch die Umweltbelastung reduzieren und langfristig Kosten senken.
Kann ich eine Single Spülmaschine selbst installieren?
Ja, in vielen Fällen ist es möglich, eine Single Spülmaschine selbst zu installieren. Die Installation einer Single Spülmaschine ist in der Regel relativ einfach und erfordert keine speziellen technischen Fähigkeiten.
Bevor Sie mit der Selbstinstallation einer Single Spülmaschine beginnen, empfehle ich Ihnen, die Bedienungsanleitung der Spülmaschine sorgfältig zu lesen und bei Unsicherheiten einen Fachmann zu konsultieren.

Hallo, Ich bin Patrick Schneider und ich bin einer aus der Experten Team von Solokitchen.
Mit über vierzig Jahren und als Single fühle ich mich in meiner gemütlichen 2-Zimmer-Wohnung wie zu Hause.
Meine Leidenschaft gilt der Küche, insbesondere Küchengeräten, die perfekt auf Einpersonen-Haushalte abgestimmt sind. In meiner bescheidenen, aber gut ausgestatteten Küche experimentiere ich gerne und teile meine Erkenntnisse und Empfehlungen mit Ihnen, um das Kochen und Genießen für Singles zu erleichtern.
Begleiten Sie mich auf einer kulinarischen Reise für Singles, während wir gemeinsam die Welt der praktischen Küchengeräte erkunden und Ihre Küche in einen Ort der Kreativität und Freude verwandeln, unabhängig von Ihrem Beziehungsstatus.